Qualys Enterprise TruRisk - SAML Relying Party Configuration - RSA Ready Implementation Guide
This article describes how to integrate RSA with Qualys Enterprise TruRisk using SAML Relying Party.
Configure RSA Cloud Authentication Service
Perform these steps to configure RSA Cloud Authentication Service as Relying Party to Qualys Enterprise TruRisk.Procedure
- Sign in to the RSA Cloud Administration Console.
- Navigate to the Authentication Clients menu, and from the dropdown, select Relying Parties.
- In the Relying Party Catalog, select Add a Relying Party and click Add for Service Provider SAML.
- On the Basic Information page, enter a name for the application in the Name field and click Next Step.
- In the Authentication tab, select SecurID manages all authentication.
- Select Access Policy as required and click Next Step.
- Provide the Service Provider details in the following format:
- Assertion Consumer Service (ACS) URL: <Qualys ACS URL>
- Service Provider Entity ID: <Qualys Entity ID>
Refer to the Qualys Enterprise TruRisk platform configuration section to obtain ACS URL and Service Provider Entity ID.
- In the SAML Response Protection section, select IdP signs assertion within response, and download the certificate by clicking Download Certificate.
- Under the User Identity section, select Show Advanced Configuration, then configure Identifier Type and Property as follows:
- Identifier Type: Auto Detect
- Property: Auto Detect
- Click Save and Finish.
- On the My Relying Parties page, click Edit dropdown and select Metadata option to download the metadata.
- Click Publish Changes to save your settings. After publishing, your application will be enabled for SSO.
Configure Qualys Enterprise TruRisk
Perform these steps to configure Qualys Enterprise TruRisk.Procedure
- Contact Qualys support: Visit www.qualys.com/support to request SAML 2.0 SSO activation for your subscription.
- Receive ACS URL and Entity ID: Qualys support will provide the ACS URL and Entity ID needed for RSA platform configuration and request the metadata file downloaded from the RSA platform.
- Configure Trust Relationship: After receiving your metadata file, Qualys support will configure the trust relationship between RSA and the Qualys platform.
- Notification of SSO Activation: Once the trust relationship is configured, Qualys support will notify you that SAML 2.0 SSO has been enabled.
- Obtain Unique URL: Qualys will provide a unique URL specific to your subscription. Users will use this URL to start a session with SAML SSO (e.g., https://qualysguard.qualys.com/fo/login.php?idm_key=XYZ).
- Extract Relay State value: The provided URL will include a key named idm_key. Copy this idm_key value for use as the relay state value in the RSA platform configuration.
- Follow these steps to obtain qualysguard_external_id:
- Log in to the Qualys Enterprise TruRisk platform with admin credentials.
- Navigate to the USERS tab.
- Select the user for whom you need the external_id and click Edit from the Quick Actions dropdown.
- Find the qualysguard_external_id in the General Information section under the External ID attribute. Use this value for the user attribute in the RSA platform, in this case ALTERNATE_USERNAME is used.
- Enable SAML SSO for the user: Click Security tab, check the Enable SAML SSO checkbox to enable SAML for the user and click Save.
Notes:
Follow these steps to add the qualysguard_external_id to RSA users:- Go to Users > Management in the RSA platform, search for the user and select them.
- Enter the qualysguard_external_id value in the appropriate user attribute (e.g., Alternate Username) and click Save.
In this case the value of qualysguard_external_id is added to the attribute ALTERNATE_USERNAME.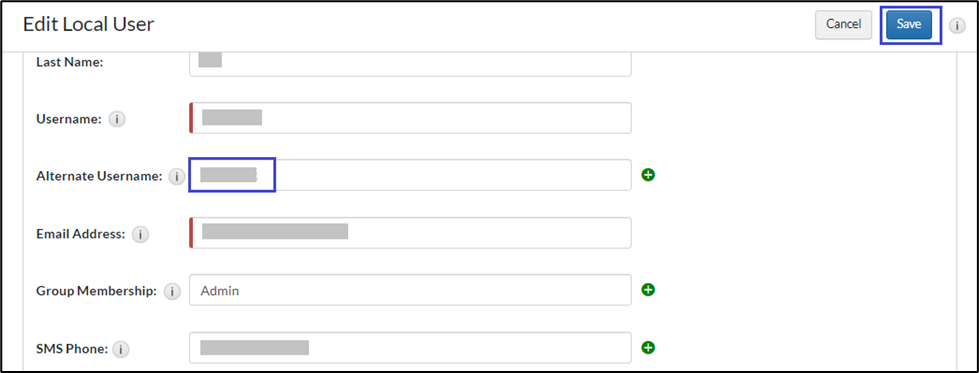
The configuration is complete.
Return to Qualys Enterprise TruRisk - RSA Ready Implementation Guide
Related Articles
Qualys Enterprise TruRisk - SAML My Page SSO Configuration - RSA Ready Implementation Guide Number of Views enVision VACollector collecting report from Qualys fails with HttpsendRequest failed: 12029 Number of Views Qualys Enterprise TruRisk - RSA Ready Implementation Guide Number of Views enVision: Webserver crashes or will not stay started Number of Views The Offline Task runtime keeps increasing Number of Views
Trending Articles
Quick Setup Guide - Passwordless Authentication in Windows MFA Agent for Active Directory RSA MFA Agent 2.5 for Microsoft Windows Installation and Administration Guide RSA MFA Agent 2.3.6 for Microsoft Windows Installation and Administration Guide How to Download OTP Token Seed Files from myRSA RSA Authentication Manager 8.9 Release Notes (January 2026)
Don't see what you're looking for?